VPN split tunneling is a powerful feature that can enhance your online experience and provide you with greater control over your internet traffic. In this guide, we will explore how VPN split tunneling works, its benefits, and how to enable it on your device.
Key Takeaways:
- VPN split tunneling allows you to route specific traffic through a VPN tunnel while bypassing the tunnel for other traffic.
- It can be configured based on specific apps or URLs, giving you control over which traffic is protected by the VPN.
- Split tunneling improves internet speed, reduces bandwidth usage, and allows simultaneous access to VPN-protected and non-VPN-protected resources.
- Enabling split tunneling depends on the VPN client software you are using and may vary across platforms.
- While split tunneling offers benefits, it is important to consider potential risks such as DNS leaks and compromised mobile devices.
What is Split Tunneling in VPN?
Split tunneling is a networking configuration that allows you to selectively route traffic through a VPN while letting other traffic bypass the VPN and use a direct internet connection. It provides the flexibility to prioritize certain apps or websites for VPN protection while maintaining fast internet speeds for non-sensitive traffic. Split tunneling can be configured by selecting specific apps or URLs to be included or excluded from the VPN tunnel, giving you control over which traffic is protected by the VPN and which traffic is not.
This configuration offers several advantages. Firstly, it improves internet speed by directing non-sensitive traffic directly to the internet, preventing it from going through the VPN server. This can be useful for activities like streaming, gaming, or accessing local resources that don’t require VPN protection. Secondly, split tunneling reduces bandwidth usage as only selected traffic is encrypted and routed through the VPN, conserving network resources. Lastly, split tunneling allows you to simultaneously access both VPN-protected and non-VPN-protected resources, providing the flexibility to use different services based on your needs.
Overall, split tunneling enhances user experience by offering the best of both worlds – the security and privacy of a VPN for selected traffic and the speed and efficiency of a direct internet connection for non-sensitive traffic. However, it’s important to configure split tunneling properly to avoid any privacy risks or security vulnerabilities. Now, let’s take a closer look at how VPN split tunneling works and its various configurations.
Key Advantages of Split Tunneling
- Improved internet speed for non-sensitive traffic.
- Reduced bandwidth usage by only encrypting selected traffic.
- Simultaneous access to both VPN-protected and non-VPN-protected resources.
Split Tunneling Configuration
Split tunneling can be configured by selecting specific apps or URLs to be included or excluded from the VPN tunnel.
By configuring split tunneling, you can prioritize certain apps or websites for VPN protection while ensuring that other traffic bypasses the VPN and uses a direct internet connection. This configuration can be done by selecting specific apps or URLs to be included in the VPN tunnel or excluding them from the tunnel. The exact steps to configure split tunneling may vary depending on the VPN client software and platform you are using.
| Configuration | Explanation |
|---|---|
| Selective App-based | Choose specific apps to either include or exclude from the VPN tunnel. |
| Inverse | Route all traffic through the VPN tunnel except for specific sources that are routed directly to the internet. |
| URL-based | Encrypt specific URLs and let the rest of the traffic pass through the internet. |
Each type of split tunneling configuration has its own advantages and can be tailored to suit your specific needs and priorities. It’s important to understand the different options available and choose the configuration that best meets your requirements.
How Does VPN Split Tunneling Work?
VPN split tunneling works by intelligently routing network traffic through either a VPN tunnel or a direct internet connection. When split tunneling is enabled, the VPN client software on your device analyzes each packet of data to determine whether it should be sent through the encrypted VPN tunnel or bypass the tunnel and use a direct internet connection. This decision is based on the configuration you have set, which can include specific apps or URLs to be included or excluded from the VPN tunnel.
The benefits of VPN split tunneling include improved internet speed for non-sensitive traffic, reduced strain on the VPN server, and the ability to access both VPN-protected and non-VPN-protected resources simultaneously. By selectively routing traffic through the VPN, you can prioritize certain apps, websites, or services for VPN protection while allowing other traffic to use a direct connection for faster speeds.
However, there are also some disadvantages to consider. Improperly configured split tunneling settings can pose privacy risks, as traffic bypassing the VPN may be exposed. Additionally, managing split tunneling configurations can be more complex compared to using a VPN with full tunneling. It is important to carefully configure and monitor split tunneling to ensure the security and privacy of your online activities.

Table: Split Tunneling Benefits and Disadvantages
| Benefits | Disadvantages |
|---|---|
|
|
Different Types of VPN Split Tunneling
VPN split tunneling offers different types of implementations that allow you to control which traffic is routed through the VPN and which traffic bypasses it. These types include app-based split tunneling, inverse split tunneling, and URL-based split tunneling.
App-based Split Tunneling
With app-based split tunneling, you have the flexibility to select specific apps that you want to include or exclude from the VPN tunnel. This means that you can prioritize certain apps for VPN protection while allowing others to use the direct internet connection. For example, you may choose to include sensitive apps like banking or email clients in the VPN tunnel for enhanced security, while excluding media streaming or gaming apps to optimize internet speed.
Inverse Split Tunneling
Inverse split tunneling takes the opposite approach. Instead of selecting which apps to include in the VPN tunnel, you choose which sources to exclude. This means that all traffic is routed through the VPN tunnel by default, except for specific sources that you identify to be sent directly to the internet. This configuration is useful if you want most of your traffic to be protected by the VPN, but still need access to certain local or trusted network resources without VPN encryption.
URL-based Split Tunneling
URL-based split tunneling allows you to encrypt specific URLs and send the rest of the traffic over the internet without VPN protection. This type of split tunneling is particularly useful if you have specific websites or web services that you want to access securely, while allowing other browsing activities to bypass the VPN tunnel. URL-based split tunneling gives you granular control over which websites receive VPN encryption, providing a balance between security and internet speed for different online activities.
How to Enable VPN Split Tunneling
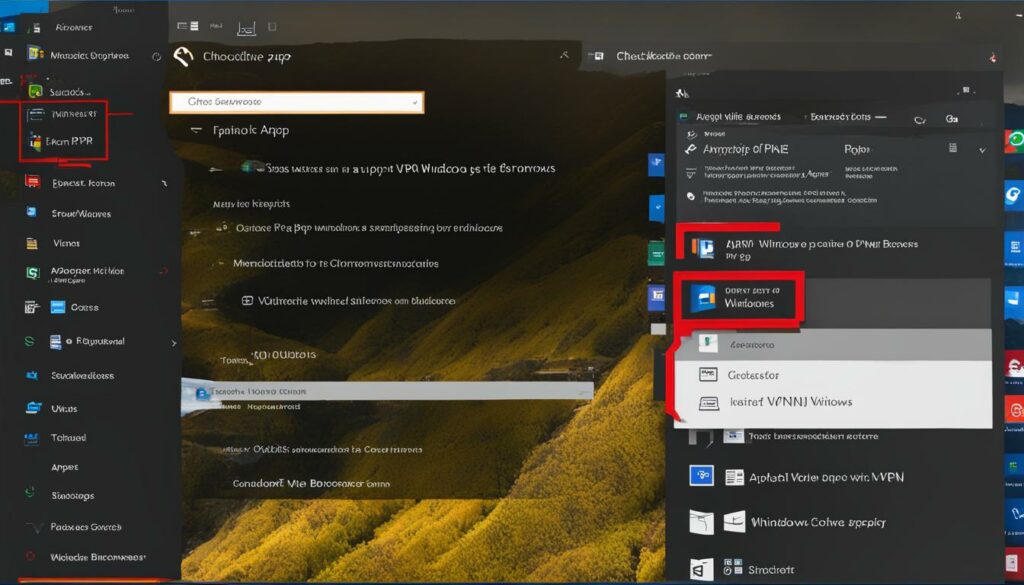
Enabling VPN split tunneling in Windows 10 is a straightforward process. Here’s a step-by-step guide on how to enable split tunneling:
- Open the “Settings” app on your Windows 10 device.
- Click on the “Network & Internet” option.
- In the left sidebar, select “VPN” from the list of options.
- Choose the VPN connection you want to enable split tunneling for. If you haven’t set up a VPN connection yet, you can do so by clicking on the “Add a VPN connection” button.
- Click on the “Advanced options” link under the VPN connection details.
- Scroll down to the “Split tunneling” section and toggle the switch to enable it.
- Once enabled, you can further customize split tunneling settings by clicking on the “Edit” button.
- In the split tunneling settings, you can choose whether to allow or block specific apps and processes from using the VPN connection.
- Click “Save” to apply the changes.
It’s important to note that the exact steps may vary depending on the VPN client software you are using. Always refer to the documentation or support resources provided by your VPN provider for specific instructions.
Windows 10 Always On VPN Split Tunnel Configuration
If you are using Windows 10 Always On VPN, the process for enabling split tunneling is slightly different. Here’s how to configure split tunneling for Always On VPN:
- Open the “Settings” app on your Windows 10 device.
- Click on the “Network & Internet” option.
- In the left sidebar, select “VPN” from the list of options.
- Choose the VPN connection you want to configure for split tunneling.
- Click on the “Change adapter options” link.
- Right-click on the VPN connection and select “Properties”.
- In the “Networking” tab, select “Internet Protocol Version 4 (TCP/IPv4)” and click on the “Properties” button.
- Click on the “Advanced” button.
- Uncheck the “Use default gateway on remote network” option.
- Click “OK” to save the changes.
Again, it’s important to consult the documentation or support resources provided by your VPN provider for specific instructions on configuring split tunneling with Windows 10 Always On VPN.
Azure Point to Site VPN Split Tunneling
Azure Point to Site VPN also supports split tunneling by default. When configuring split tunneling for Azure Point to Site VPN, you can specify which traffic should go through the VPN and which traffic should bypass the VPN. This allows you to access both VPN-protected and non-VPN-protected resources simultaneously. Consult the Azure documentation for detailed instructions on how to enable split tunneling for Azure Point to Site VPN.
VPN Split Tunneling Protocols
VPN split tunneling is supported by various VPN protocols, including OpenVPN, L2TP/IPSec VPN, PPTP VPN, SSTP VPN, IKEv2 VPN, and WireGuard VPN. These protocols provide the underlying technology for establishing secure connections and encrypting data. The specific protocol used by your VPN client may depend on the VPN service provider you are using.
| Protocol | Description |
|---|---|
| OpenVPN | A popular open-source protocol known for its strong security and flexibility. |
| L2TP/IPSec VPN | A protocol that combines the benefits of Layer 2 Tunneling Protocol (L2TP) and Internet Protocol Security (IPSec) for secure communication. |
| PPTP VPN | A protocol that offers relatively fast speeds and compatibility with a wide range of devices. |
| SSTP VPN | A protocol that uses Secure Socket Tunneling Protocol (SSTP) to provide secure communication over the internet. |
| IKEv2 VPN | A protocol that offers excellent security and stability, especially for mobile devices. |
| WireGuard VPN | A newer protocol that offers high-speed performance and streamlined code. |
Each protocol has its own advantages and can be used depending on your specific needs and preferences. It is important to choose a VPN service provider that supports the protocol you prefer and offers the level of security and performance you require. By understanding the different VPN split tunneling protocols, you can make informed decisions to ensure the privacy and security of your online activities.
VPN Split Tunneling Risks
While VPN split tunneling can offer many benefits, it also comes with certain risks that users should be aware of. Understanding these risks can help you make informed decisions when configuring and using split tunneling.
Risk of a DNS Leak
One potential risk of VPN split tunneling is the possibility of a DNS leak, where DNS requests made by your device bypass the VPN tunnel and are sent directly to your Internet Service Provider (ISP). This can potentially expose your browsing activity and compromise your privacy. It is important to ensure that your VPN client is properly configured to prevent DNS leaks and protect your online anonymity.
Compromised Mobile Devices
Another risk associated with split tunneling is the potential for compromised mobile devices. When split tunneling is enabled, certain traffic is allowed to bypass the VPN’s security measures, which can leave your device vulnerable to attacks. It is crucial to maintain the security of your mobile devices and regularly update their operating systems and security software to mitigate this risk.
Poor Configuration
Poor configuration of split tunneling settings can also pose risks to your online security. If not properly configured, split tunneling can lead to unintended data exposure or create security vulnerabilities. It is important to carefully configure and monitor your split tunneling settings to ensure that your sensitive traffic is protected and your non-sensitive traffic is not putting your security at risk.
Table: VPN Split Tunneling Risks Summary
| Risk | Description |
|---|---|
| Risk of a DNS Leak | DNS requests bypass the VPN tunnel, potentially exposing browsing activity and compromising privacy. |
| Compromised Mobile Devices | Split tunneling allows certain traffic to bypass VPN security measures, increasing the risk of device compromise. |
| Poor Configuration | Improperly configured split tunneling settings can lead to data exposure and security vulnerabilities. |
“VPN split tunneling can provide convenience and efficiency, but it’s important to understand the associated risks. By being aware of the potential for DNS leaks, compromised mobile devices, and poor configuration, users can take the necessary steps to mitigate these risks and ensure a secure online experience. Configuring split tunneling settings carefully and regularly updating mobile devices can help maintain a strong layer of defense against potential threats.”
Incorporating VPN Split Tunneling with Perimeter 81
Perimeter 81 offers a secure Network as a Service (NaaS) solution that enables organizations to incorporate VPN split tunneling into their network infrastructure. With Perimeter 81’s NaaS, you can provide secure remote access to your network resources while conserving bandwidth and improving internet speed. The split tunneling feature allows you to access multiple networks at once, ensuring that sensitive traffic is routed through the VPN tunnel while allowing general internet traffic to bypass the tunnel. This enhances security and efficiency for remote workers and organizations.
| Benefits of Incorporating VPN Split Tunneling with Perimeter 81 |
|---|
| Secure Remote Access |
| Perimeter 81’s NaaS provides a secure way for remote workers to access network resources and applications, without compromising sensitive data. Split tunneling ensures that only the necessary traffic is routed through the VPN tunnel, protecting it from potential threats. |
| Conserving Bandwidth |
| By allowing non-sensitive traffic to bypass the VPN tunnel, you can conserve bandwidth and improve internet speed for general browsing and non-critical activities. This ensures optimal performance for both remote workers and the network. |
| Access Multiple Networks at Once |
| Perimeter 81’s split tunneling feature enables remote workers to access multiple networks simultaneously. This flexibility allows for efficient collaboration and seamless access to resources on different networks without compromising security. |
By incorporating VPN split tunneling with Perimeter 81, organizations can achieve secure remote access, conserve bandwidth, and access multiple networks at once. This enhances productivity and efficiency for remote workers while maintaining the highest level of security for sensitive data. Perimeter 81’s NaaS solution provides a comprehensive and user-friendly platform for implementing and managing split tunneling, ensuring a seamless and secure remote work experience.
Conclusion
VPN split tunneling is a valuable feature that enhances your online experience by providing control over which traffic is encrypted through a VPN tunnel and which traffic bypasses it. By understanding how VPN split tunneling works, you can prioritize your sensitive data while still enjoying fast internet speeds and efficient access to non-sensitive resources.
Split tunneling in VPN allows you to strike the right balance between security and convenience. By selectively routing specific apps or URLs through the VPN tunnel, you can ensure that your sensitive information remains protected while allowing other traffic to use a direct internet connection. This flexibility is particularly useful for accessing apps, websites, or services that may not be VPN-friendly or require faster internet speeds.
Implementing split tunneling in your VPN configuration involves configuring your VPN client software to include or exclude specific apps or URLs from the VPN tunnel. This configuration can vary depending on the VPN client and platform you are using. By taking advantage of this feature, you can optimize your network performance and make informed decisions about securing your online communications.
In summary, VPN split tunneling provides a versatile solution to meet your specific needs in terms of security, privacy, and internet speed. By understanding how it works and its various configurations, you can make the most of your VPN and enjoy a seamless online experience.
FAQ
What is VPN split tunneling?
VPN split tunneling is a feature that allows you to route specific traffic through an encrypted VPN tunnel while allowing other traffic to bypass the tunnel and use a direct internet connection.
How does VPN split tunneling work?
VPN split tunneling works by intercepting network traffic from your device and intelligently routing it through either the VPN tunnel or the open internet based on the configuration you have set.
What are the advantages of VPN split tunneling?
The advantages of VPN split tunneling include improved internet speed, reduced bandwidth usage, and the ability to access both VPN-protected and non-VPN-protected resources simultaneously.
What are the different types of VPN split tunneling?
The different types of VPN split tunneling include app-based split tunneling, inverse split tunneling, and URL-based split tunneling.
How can I enable VPN split tunneling?
Enabling VPN split tunneling depends on the specific VPN client software you are using. The exact steps may vary depending on the client and platform, but generally involve editing the properties of your VPN connection.
Which VPN protocols support split tunneling?
VPN split tunneling is supported by various VPN protocols, including OpenVPN, L2TP/IPSec VPN, PPTP VPN, SSTP VPN, IKEv2 VPN, and WireGuard VPN.
What are the risks of VPN split tunneling?
The risks of VPN split tunneling include potential DNS leaks, compromised mobile devices, and the need for proper configuration to avoid data exposure or security vulnerabilities.
How can I incorporate VPN split tunneling with Perimeter 81?
Perimeter 81’s Network as a Service (NaaS) solution allows you to incorporate VPN split tunneling into your network infrastructure, providing secure remote access while conserving bandwidth and improving internet speed.